The weekly round-up blog posts will take a look at my favorite bits of news over this week!
This week, we look at the Timehop Data Breach, the “Right Hand” Hackers, Jail time for a cyber attack on the National Lottery and the manuals for a US Military Drone for sale on the Dark Web.
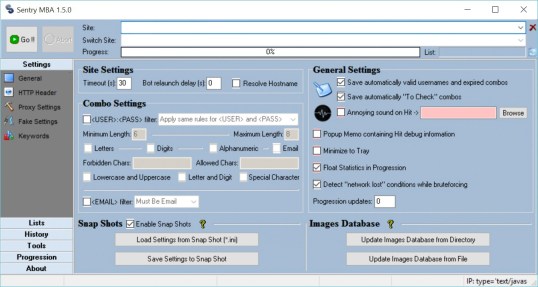
“The hacking programme Sentry MBA was used to retrieve username and password combinations, which were sold on or supplied to hackers“. — BBC News
Before Facebook built-in the “On This Day” feature into its global social networking platform, Timehop was all the rage. I can recall scrolling though my Facebook timeline aimlessly looking at what embarrassing photos my friends had reproduced to the spotlight. However, earlier this week, Timehop announced they have had a data breach effecting 21 million users.
The data stolen from the nostalgic firm included; Names, Email Addresses, Phone Numbers and the application keys used to collect your social media posts from the past. There is no evidence that any account was accessed using the stolen keys during the attack.
What is most interesting about this breach, is that this was not a retrospective detection. The company claims that there were made aware of the breach whilst it was in progress and were able to interrupt and stop the attacker going any further;
“On July 4, 2018, Timehop experienced a network intrusion that led to a breach of some of your data,” a statement from Timehop “We learned of the breach while it was still in progress, and were able to interrupt it, but data was taken.” – Timehop Statement
The breach occurred due to an account, or credentials for an account used on a cloud platform were compromised. Timehop themselves even state that there was no multifactor authentication protecting the account onto the cloud platform.
Yet another incident where basic Cloud Security controls were not implemented. A hot topic in itself at this moment in 2018.

The BBC this week posted and article headlined “Phone in the right hand? You’re a Hacker!”
The article looks at how the common or traditional security defences are not enough anymore to stop well organised and targeted attacks, such as BOTNET and AI Powered attacks.
Big business are collecting vast amounts of data to not only impact sales or marketing campaigns, but also to identify if you are a human at the end of the device. Botnet and AI powered attacks are on the rise, being able to identify and differentiate between these bots can help prevent malicious activity on the platform.
Now software can look into how you use your device, such as inputting your username and password. It looks at how fast you are typing, the mistakes you make and even HOW YOU ARE HOLDING YOUR PHONE, something that was recently demoed to me. Typically a humans typing patterns are like a signature, uniquely identifiably to you. However, as a BOT cannot mimic this, the patters of typing are very static and do not change.
So even though the BBC headline would state that I am a hacker, it’s really looking into how companies are now having to understand user behaviour data to better protect them from the BOTs.
This leads nicely into further news reported by the BBC that two hackers who used a botnet type attack against the National Lottery have been jailed.
The attackers used popular credential stuffing tool SentryMBA, to crack user accounts on the national lottery website.
SentryMBA, uses botnets to fire authentication attempts for a pre-defines list of usernames and passwords (often taken from known, previous breaches) against the sign-in page of a website. If an account is compromised they are often sold to criminals on the dark web.
The court heard that one of the defendants had been seen watching “Hacking Tutorials” online shared by another hacker.
One of the defendants was sentenced to 8 months on the inside, with the other walking away with just 4. Tough enough sentence? Maybe not. However a great win for the authorities.
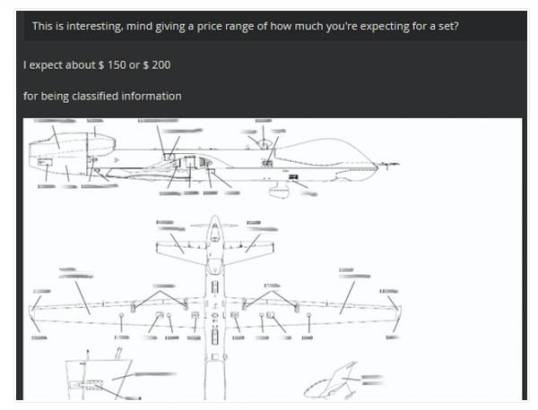
Lastly, in the news this week we learn that sensitive and classified information pertaining to an US Military Drone has been seen on the dark web up for auction.
This comes after cyber security firm Recorded Future claim they engaged with the “newly registered English-speaking hacker” to validate the compromised documents. These documents included a M1 Abrams tank maintenance manual, a tank platoon training course, a crew survival course, and documentation on how to avoid the use of an Improvised Explosive Device (IED).
Recorded Future have stated “The attacker used a widely known tactic of gaining access to vulnerable Netgear routers with improperly setup FTP login credentials”
All of this information was made available by compromising the computer of an US Military Captain who had not set a password for a “secure” FTP site holding the sensitive data.
The irony here is that, an article in the register claims, that the Captain has recently completed Security User Awareness Training.
That concludes this weeks, Weekly Round-up. Be sure to sign up to see next weeks!
References:
https://www.theregister.co.uk/2018/07/11/us_military_manual_dark_net_sale/
https://www.bbc.co.uk/news/uk-england-44819915
https://www.bbc.co.uk/news/technology-44438808
https://www.timehop.com/security
https://www.akamai.com/uk/en/products/cloud-security/bot-manager.jsp